You may have heard the terms phishing, smishing or vishing before, but what exactly do they mean?
At their core, all three terms are a type of financial fraud which tricks unsuspecting victims into giving out sensitive personal information, handing over money or installing malware onto their device.
The only difference between each term is the channel via which you can be targeted; phishing refers to scam emails, smishing refers to scam text or WhatsApp messages and vishing takes place over the phone.
Phishing
The most common phishing method encourages victims to visit a malicious website through a fake email message, which appears to be sent from a legitimate company or source (e.g. from a bank, HMRC, a delivery company or the NHS).
For example, you might receive an email which appears to be from an organisation who you’re familiar with, asking you to click on a link. At this point you will be taken to a webpage on which you’re asked to submit sensitive data, such as passwords, usernames or bank details. This might sound like an obvious trick, but cyber criminals are highly adept at creating authentic looking emails and fake websites which lull victims into a false sense of security as they can look just like the real thing.
Another common method of attack uses emails that appear to come from a legitimate source, but include attachments containing dangerous software (otherwise known as ‘malware’) which could be capable of stealing personal information. The attachment might be labelled as ‘receipt’, ‘invoice’ or something equally enticing to encourage you to open it, at which point the malware is downloaded onto your device.
Smishing
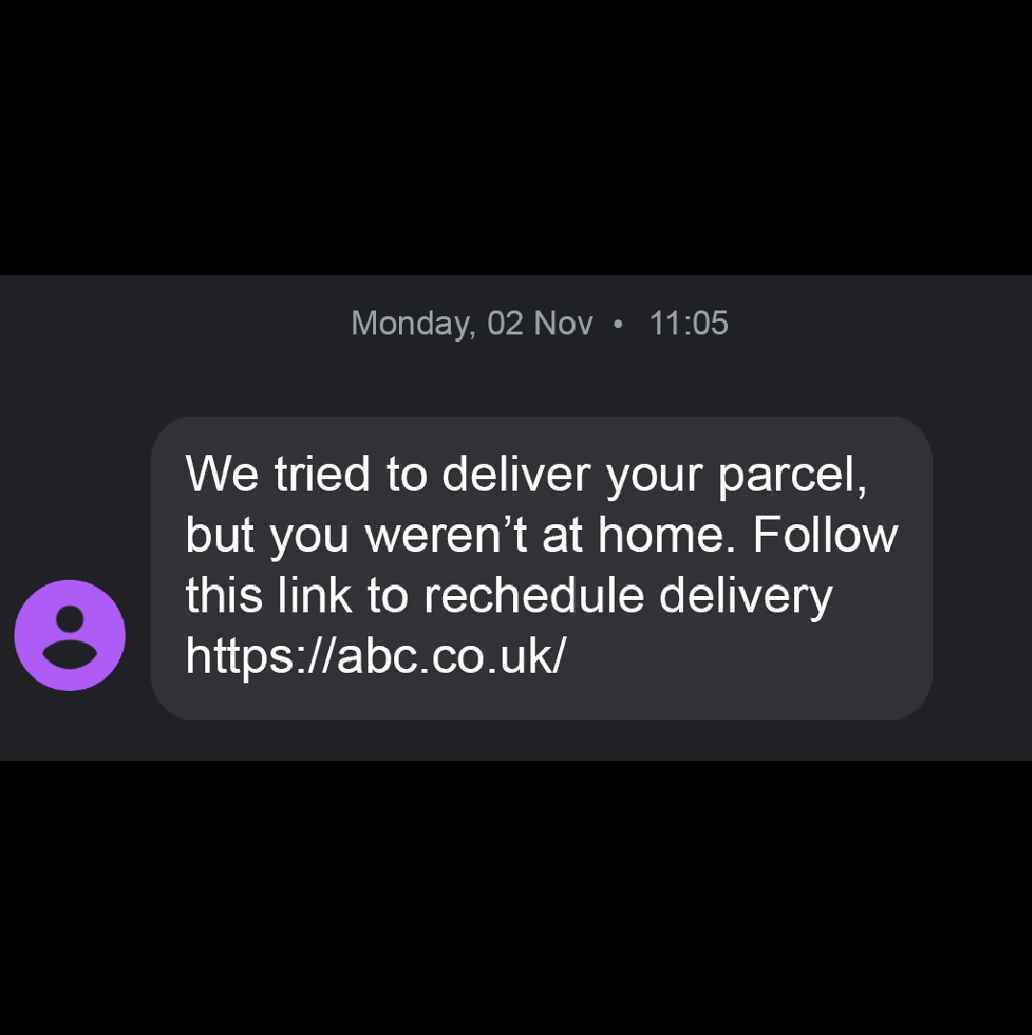
Smishing follows largely the same pattern as phishing but it takes place over text (also known as SMS) or messaging services like WhatsApp.
For example, you might have heard of the recent Royal Mail scam, in which thousands of people around the UK received a fake text message claiming that payment was required in order for a package to be delivered. Recipients of the message were instructed to click on a link, directing them to a fraudulent website which collected personal and payment details.
Vishing
Unlike phishing or smishing, vishing refers to over-the-phone fraud where criminals will call you, posing as your bank or another seemingly reputable company, in order to verbally obtain sensitive data such as passwords, addresses and so on.
You may be familiar with the recent HMRC vishing scam, in which fraudsters used an automated phone call to convince victims that they had unpaid tax bills to settle, conning them out of hundreds of pounds. In this particular case the criminals were able to mimic the official HMRC number and used the threat of filing a lawsuit against the victims to scare them into making the payment.
How to protect yourself
Follow these helpful dos and don’ts to prevent yourself from becoming a victim of a phishing attempt…
Don't
- Disclose any card security details, like your PIN number, Internet Banking log in details or card number, over the phone, by email or text message or via a link included in an email or text.
- Feel rushed or pressured into making a decision. No genuine bank or other legitimate organisation would ask you to carry out a transaction on the spot.
- Assume that an email, phone call or text message is authentic. If in doubt hang up the phone or delete the email or text message without opening it.
- Click on links or attachments included in unsolicited emails or text messages.
Do
- Call companies back using the number on their website. If you are unsure whether a phone call, email or text message request is genuine, it always best to call the organisation back using the number on its website to confirm.
- Check email addresses, phone numbers and URLs carefully – do they look suspicious?
- Install up-to-date anti-virus software on your devices.
- Follow the ABC framework for fraud: Accept nothing, Believe no-one and Confirm everything.
- Get link
- X
- Other Apps
- Get link
- X
- Other Apps
Comments
Post a Comment